SharePoint Online
This page will list security settings and configurations that is advisable to implement in your environment.
Each environment is different where I believe the below settings are easy to setup and provides a way to get to a more mature security level.
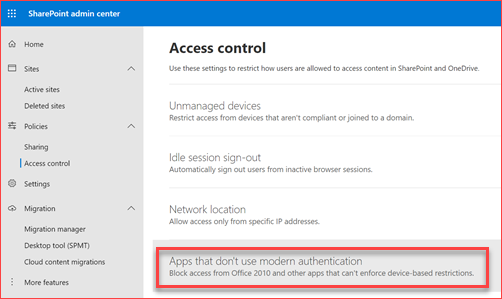
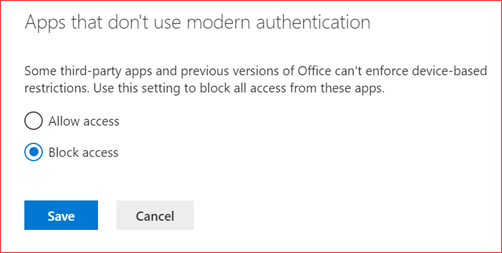
Enforce modern authentication
Modern authentication makes it able to logon using multi-factor authentication, smartcard or using certificates. It is advisable to enforce modern authentication if possible. Multi-factor authentication can be circumvented if basic authentication is still allowed. Should the need arise to allow basic authentication you can also use conditional access to further protect the environment to only allow some users from some locations using basic authentication.
How will this impact my users?
Users will no longer be able to use older or third party applications that only work with basic authentication like Office 2010.
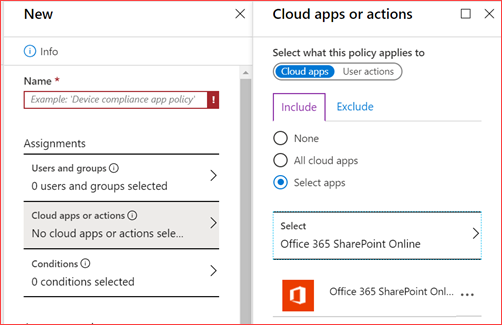
Using conditional access
You can use conditional access to block access when basic authentication is used or allow access for basic authentication applications. Click here for the direct link.
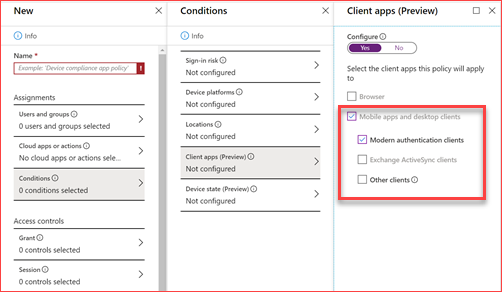
Create a new policy and select a group which has all or some of the users. Preferably a dynamic group. And then select for which application this policy applies. In my case I select SharePoint Online.
Then under conditionals you can select the authentication client this application can or cannot use. Under Access controls you can block or allow this policy.
Using PowerShell
You will need to install the SharePoint Online module to be able to use the below CMDlets. Run the below CMDlets to enable modern authentication for your SharePoint Online environment.
Connect-SPOService
Set-SPOTenant -LegacyAuthProtocolsEnabled $false
SharePoint Online sharing
It is important to verify if the sharing settings are in line with the organization. It is by default possible to share documents or sites with everyone and that guests are able to share documents they don’t own. You can also enable sharing for SharePoint but disable sharing for OneDrive. We advise to allow sharing to guest users but require them to sign in or use a verification code. It is possible to restrict guest invites to only users with the guest inviter role but depending on the organization it can be a lot of work to manage this. Disable guests to share items they do not own and enforce guests must sign in using the same account to which sharing invitations are sent.
How will this impact my users?
It depends on the configuration but the configuration below will have little impact for users as they are able to share documents and sites with everyone by adding them as a guest to the Azure Active Directory. Users will need to issue a ticket to the correct support group should adding guests is only allowed for users with the guest inviter role.
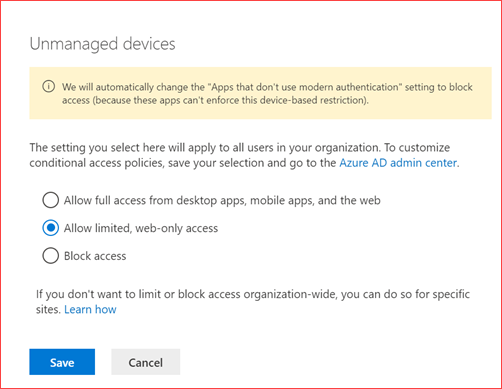
Restrict access from non compliant devices
SharePoint and Exchange Online have the possibility to restrict users from non compliant devices. In SharePoint this will restrict users from downloading, printing and synchronizing sites and documents. Teams and OneDrive uses SharePoint Online so this policy also applies for the documents that are located there. You will need to have Azure Active Directory premium and Intune license as you also need to create an conditional access policy. This is especially helpful when sharing SharePoint with guest users as they also can’t download, print or sync these documents. They are only able to view and edit the document in the browser.
How will this impact my users?
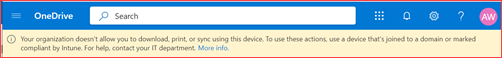
Users will no longer be able to download, print or synchronize documents from everywhere as it will require a compliant device. When using Intune you can setup your own rules to be sure that content is being secured and managed. They will see the below message.
Your organization doesn’t allow you to download, print or sync using this device. To use other actions, use a device that’s joined to a domain or marked compliant by Intune. For help, contact your IT department.
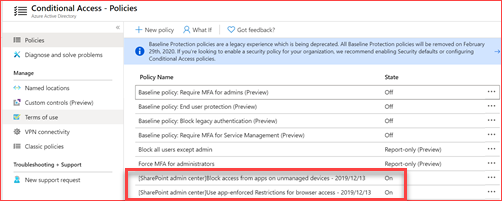
Using conditional access
A conditional access policy will automatically be created in the Azure Active Directory which you can customize if needed . You may want to exclude certain service accounts or want to allow this policy on company devices which are located on-premises. Click here for the direct link.
We suggest you change the name to your naming convention and it’s possible to also add Exchange Online to the same policy where we will add this in the Exchange Online page.